Operating system: Windows, Android, macOS
Group of programs: Business automation
Organization of accounting of security
- Copyright protects the unique methods of business automation that are used in our programs.

Copyright - We are a verified software publisher. This is displayed in the operating system when running our programs and demo-versions.

Verified publisher - We work with organizations around the world from small businesses to large ones. Our company is included in the international register of companies and has an electronic trust mark.

Sign of trust
Quick transition.
What do you want to do now?
If you want to get acquainted with the program, the fastest way is to first watch the full video, and then download the free demo version and work with it yourself. If necessary, request a presentation from technical support or read the instructions.

Contact us here
How to buy the program?
View a screenshot of the program
Watch a video about the program
Download demo version
Compare configurations of the program
Calculate the cost of software
Calculate the cost of the cloud if you need a cloud server
Who is the developer?
Program screenshot
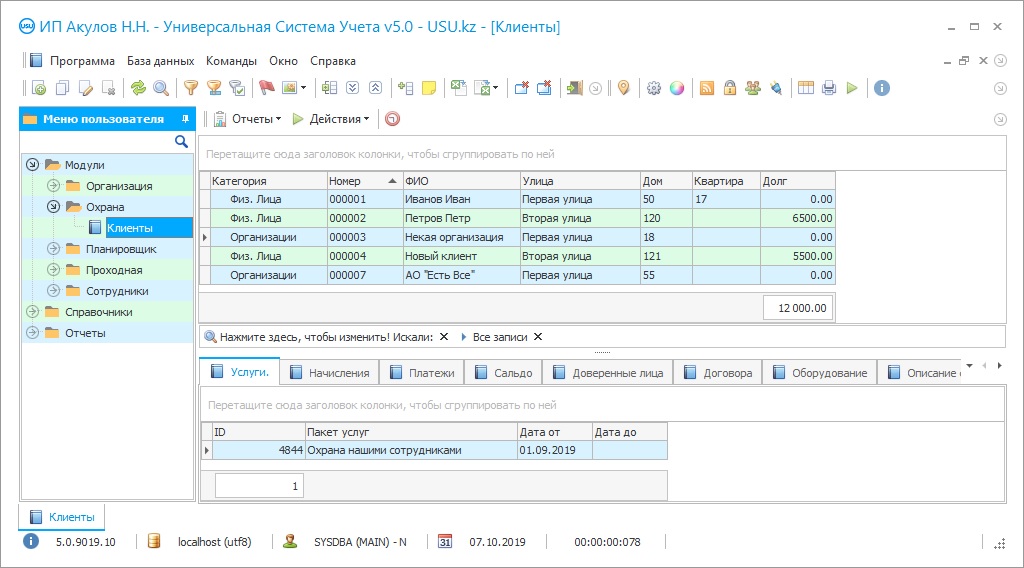
The organization of the security of a modern enterprise requires a systematic approach, appropriate professional qualifications, and, oddly enough, possession of modern IT technologies. There is a fairly wide range of software solutions on the market that automate many of the security organization's work processes. However, if the company is large enough, has a large staff of qualified employees, and simultaneously works with several customers, protecting and protecting their interests, the best solution would be either to develop a custom-made control system or to purchase a modular program with ample opportunities for revision and development of control subsystems. As the scope of the security agency expands, the number of clients, staff, and so on, will change the requirements for the software. Therefore, it is better to take care in advance that the set of its functions is not strictly limited and can be improved. Today, professional security is impossible without the use of various technical devices, the range of which is limited only by the financial capabilities of the customer. The computer control system must ensure the integration of various sensors, alarms, electronic locks, turnstiles, navigators, etc., operational accounting, and adequate response to signals coming from them.
USU Software has developed its own unique accounting product, with the help of which the security organization is maintained in modern conditions. All information generated by departments during the protection of objects for all types of services is accumulated in a single database, classified according to the selected parameters, and can be used to analyze work results, build plans, forecasts, etc. suppliers of equipment and consumables, service companies, subcontractors, and so on, containing up-to-date contact information and a complete history of all relationships, dates, and terms of contracts, key conditions, cost of services, and so on. The built-in scheduler allows you to plan work for each guarded object separately, create work plans for individual employees, monitor their implementation, program database backups, configure the parameters of analytical reports, etc. Accounting tools provide the accounting of the security company with the ability to control the overall accounting, cash flow, settlements with customers and suppliers, manage accounts receivable, adjust the tariff scale, organize charges with one-time services, and so on.
Who is the developer?
Akulov Nikolay
Expert and chief programmer who participated in the design and development of this software.
2024-05-12
Video of organization of accounting of security
This video can be viewed with subtitles in your own language.
Filling and printing of standard documents, receipts, invoices, order forms, and others, is carried out automatically. For each object, a list of trusted persons of customers is formed with the indication of contact information, scanned copies of documents are attached. The program includes special forms for scheduling duty shifts, developing routes bypassing the territory, schedules for patrols. The work of the security organization with the help of the USU Software is carried out in the most optimal way, the company's resources are used with maximum efficiency. Reducing operating costs provides an overall increase in business profitability, strengthening the company's position in the market, customer loyalty, and the image of a reliable, professional organization.
Organization of security using the USU Software is carried out with maximum efficiency. The program is configured individually, taking into account the peculiarities of the company and the specifics of the protected objects. Accounting and control within the system are carried out for any number of objects of protection. The built-in electronic checkpoint ensures strict adherence to the access control regime approved by the organization. The program provides for integration with the latest security technologies and modern technical devices, sensors, cameras, proximity tags, electronic locks, etc., used by the security service. Automated business processes and accounting procedures allow you to save working time, improve the level of organization of business processes in the company.
Download demo version
The customer database is created and updated centrally, contains all the contact information necessary for successful work with customers. Digital maps of all protected objects are integrated into the program, allowing you to quickly navigate in a working situation, adequately respond to various incidents, and maintain the necessary records. The location of each security officer is marked on maps.
Each actuation of alarm systems is quickly recorded and a work task is automatically created for the corresponding employee of the organization.
Order an organization of accounting of security
To buy the program, just call or write to us. Our specialists will agree with you on the appropriate software configuration, prepare a contract and an invoice for payment.
How to buy the program?

The program will be installed
If the program is purchased for 1 user, it will take no more than 1 hourBuy a ready-made program
Also you can order custom software development
If you have special software requirements, order custom development. Then you won’t have to adapt to the program, but the program will be adjusted to your business processes!
Organization of accounting of security
Thanks to the built-in cameras at the checkpoint, you can print one-time and permanent passes for visitors, badges for employees with photos attached. An electronic checkpoint accounting program registers the date, time, purpose of the visit of unauthorized persons, the duration of their stay at the facility, the receiving unit, etc. Data on the accounting of individual projects, the protection of facilities, etc. are accumulated in a single database. The complex accounting reports for the director of the organization provide up-to-date reliable information on the processes related to security, for the analysis and evaluation of work results. By an additional order, the program activates mobile applications for customers and employees in order to increase the speed of information exchange and accelerate interaction. If necessary, payment terminals, automatic telephone exchange, a special application for managers can be integrated.