Operating system: Windows, Android, macOS
Group of programs: Business automation
Security optimization
- Copyright protects the unique methods of business automation that are used in our programs.

Copyright - We are a verified software publisher. This is displayed in the operating system when running our programs and demo-versions.

Verified publisher - We work with organizations around the world from small businesses to large ones. Our company is included in the international register of companies and has an electronic trust mark.

Sign of trust
Quick transition.
What do you want to do now?
If you want to get acquainted with the program, the fastest way is to first watch the full video, and then download the free demo version and work with it yourself. If necessary, request a presentation from technical support or read the instructions.

Contact us here
How to buy the program?
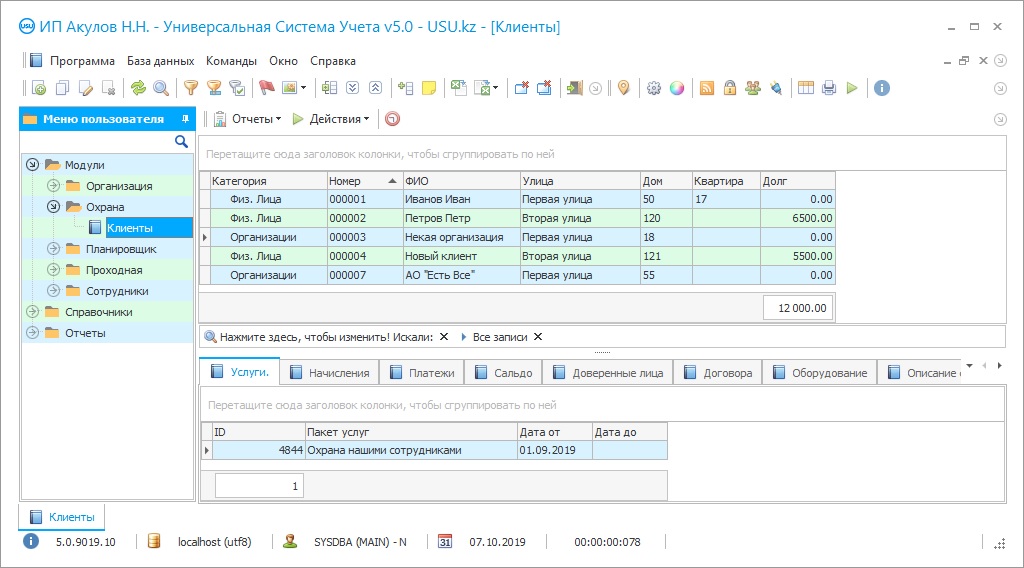
View a screenshot of the program
Watch a video about the program
Download demo version
Compare configurations of the program
Calculate the cost of software
Calculate the cost of the cloud if you need a cloud server
Who is the developer?
Program screenshot
Optimization of security by the meaning of this term involves the adoption of measures aimed at increasing the overall efficiency of the security service while reducing non-productive costs and costs of its maintenance, information, and technical support, a security agency with the appropriate permits and licenses, instead of creating its unit. In this case, a lot of legal and financial issues, personnel problems, are immediately removed for the company. Optimization of security maintains by attracting a professional company practically guarantees that professionals in their field engaged in protecting your interests, whom it would be very difficult for you to find on your own. Another way to conduct optimization is the selection and implementation of specialized software that automates key work processes and reduces personnel costs due to the widespread use of various technical devices. The result, as a rule, is a general improvement in the quality of services, the accuracy of recording various events and incidents, the speed and adequacy of the response.
Who is the developer?
Akulov Nikolay
Expert and chief programmer who participated in the design and development of this software.
2024-05-11
Video of security optimization
This video can be viewed with subtitles in your own language.
USU Software system offers its unique product that guarantees security services optimization. The program can be used with equal efficiency by commercial or state enterprises, agencies specializing in the protection of various objects. The USU Software has an electronic checkpoint in its structure, which allows accurately recording the working time of employees (late arrivals, overtime, smoke breaks), issue passes to visitors, and control their movement around the protected area (date, time, the purpose of the visit, duration of stay, receiving unit). One-time and permanent passes can be printed directly at the entrance with the attachment of the visitor's photo. All information is stored in a single database and can be used to prepare summary reports on employees and guests of the company, analyze the dynamics of visits, control labor discipline, etc. The program provides the ability to integrate modern technologies, devices, and devices (motion sensors, burglar alarms, card locks, electronic turnstiles, navigators, proximity tags, video surveillance cameras) related to the protection and protection of territory maintenance, material, financial, information resources, etc. The built-in map provides optimization of the control of the territory and the on-duty bypass routes. The program contains a scheduler that allows setting up backup information, parameters of analytical reports, etc. The company's management has the ability to quickly form a schedule of duty shifts, plan the protection of individual rooms and territories. The accounting of each object's authorized persons is carried out centrally. Accounting tools provide the ability to control security services settlements, manage accounts receivable, promptly generate invoices, etc.
Download demo version
Optimization of security within the framework of the USU Software is ensured through the automation of basic processes, transparency of accounting procedures, and the integration of the latest security technologies.
Order a security optimization
To buy the program, just call or write to us. Our specialists will agree with you on the appropriate software configuration, prepare a contract and an invoice for payment.
How to buy the program?

The program will be installed
If the program is purchased for 1 user, it will take no more than 1 hourBuy a ready-made program
Also you can order custom software development
If you have special software requirements, order custom development. Then you won’t have to adapt to the program, but the program will be adjusted to your business processes!
Security optimization
The specialized USU Software program ensures the optimization of security services for both commercial enterprises and professional agencies. The system is configured individually, taking into account the specifics of the activities and services of the customer and the objects offered for protection. Due to the fact that work processes and accounting are automated, the platform is an effective managing security activities tool.
The USU Software contains a built-in electronic checkpoint, which can be adjusted following the approved checkpoint regime at the enterprise. Integration of the latest technologies used to optimize security increases the efficiency of the system. The built-in database of counterparties is created and maintained centrally, contains complete information on interaction with each customer. The signals from the alarm sensors (burglar, fire, etc.) are sent to the central control panel of the duty shift. The built-in map provides the ability to quickly localize alarms, send the nearest patrol group to the scene, and optimize emergency prevention measures. Accounting tools provide company managers with the ability to control the settlement of services, manage accounts receivable, set up a tariff scale, calculate piecework wages, etc. The program generates work plans and lists of the unlimited number of objects of protection tasks, and also provides the ability to monitor their implementation. The electronic checkpoint provides a recording of each entrance and exit of the company's employees using a barcode scanner of a personal pass, optimization of labor discipline control. Based on the generated employee database, it is possible to generate each employee individual reports, indicating the number of his delays, overtime, etc. Optimization of the checkpoint operation ensures strict registration of visitors, the printing of one-time passes with attached photos, and subsequent analysis of the dynamics of visits. The complex of the director of a security company management reports provides complete information about the current state of affairs and the results of the company's (primarily related to security services) analyzing the situation activities and making competent management decisions. As part of an additional order, integration into the program of an automatic telephone station, payment terminals, mobile applications for employees and customers, etc.